Darknet Markets 2026:
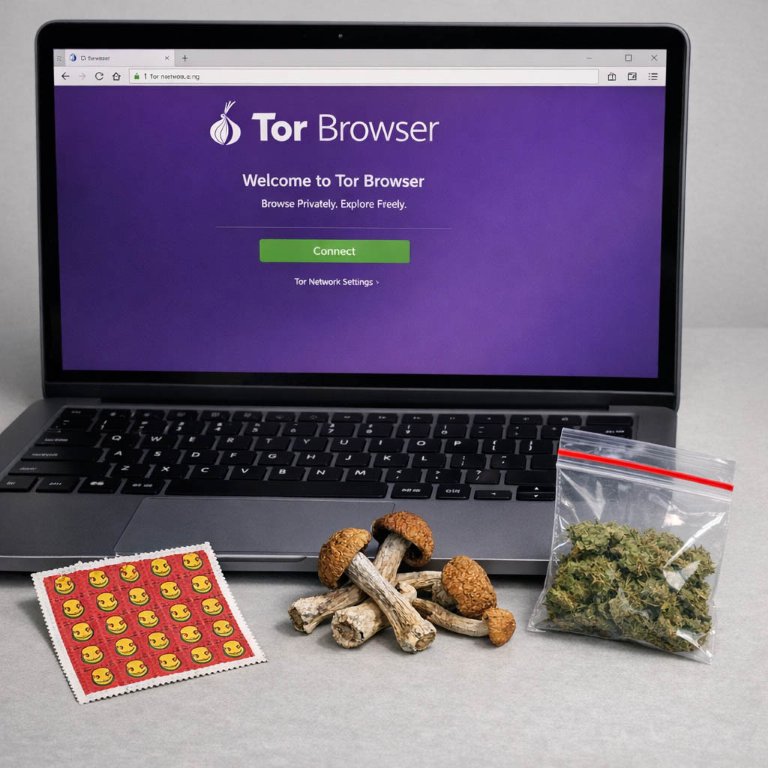
The dark web is part of the deep web but is built on darknets: overlay networks that sit on the internet but which can't be accessed without special tools or software like Tor. Tor is an anonymizing software tool that stands for The Onion Router — you can use the Tor network via Tor Browser.
| Darknet Market | Established | Total Listings | Link |
|---|---|---|---|
| Nexus Market | 2024 | 600+ | Onion Link |
| Abacus Market | 2022 | 100+ | Onion Link |
| Ares | 2026 | 100+ | Onion Link |
| Cocorico | 2023 | 110+ | Onion Link |
| BlackSprut | 2023 | 300+ | Onion Link |
| Mega | 2016 | 400+ | Onion Link |
Updated 2026-06-04
How Encrypted Networks Build Reliable Darknet Commerce
The operational foundation of a darknet marketplace is its existence on an encrypted, anonymizing network, primarily the Tor network. This infrastructure provides the necessary layer of separation between the server hosting the marketplace and the public internet, shielding its physical location and the IP addresses of its users. This architectural choice is fundamental, as it creates a persistent digital space where commerce can occur outside the visibility of conventional web indexing and surveillance.
This encrypted foundation enables the core marketplace functions:
Vendor shops can be established with a significant degree of operational security.
Buyers can browse listings without revealing their network location.
All communications, from order placement to dispute resolution, are routed through this protected channel.
The stability and longevity of a marketplace are directly tied to the robustness of this foundation. A well-implemented hidden service resists takedowns and maintains consistent uptime, which in turn fosters user trust and vendor retention. The technical implementation often includes:
- Regularly updated Tor hidden service addresses to mitigate denial-of-service attacks.
- Integration of PGP encryption for all private messages, ensuring that even platform administrators cannot read sensitive communication.
- Redundant infrastructure to handle high traffic and maintain availability.
Consequently, the encrypted network is not merely a gateway but the essential substrate upon which the entire ecosystem of anonymous e-commerce is built, determining its resilience and capacity for secure, private transactions.
How Privacy Tools Make Darknet Commerce Safe and Reliable
The operational integrity of a darknet marketplace is fundamentally dependent on its ability to guarantee user anonymity. This is not a secondary feature but the primary mechanism that enables the ecosystem to function. Anonymity is achieved through a layered technological approach, starting with network access via the Tor browser, which obfuscates a user's IP address and physical location. This initial layer ensures that the act of connecting to the marketplace itself is private.
Within this encrypted space, transactions are designed to sever the link between personal identity and financial activity. This is where cryptocurrencies, primarily Bitcoin and Monero, become essential. They act as digital cash, allowing value transfer without the involvement of traditional financial institutions that require personal identification. Monero, in particular, offers enhanced privacy features by default, making transactions opaque and untraceable on its blockchain, which is often preferred for its superior anonymity over the pseudo-anonymous and transparent Bitcoin ledger.
The transaction process itself is structured to minimize data exposure:
- Vendors never receive a buyer's home address in plain text. Instead, shipping details are communicated using PGP encryption, where only the vendor's private key can decrypt the information.
- Marketplace administrators act as facilitators rather than holders of sensitive data, as the encrypted messages pass directly between the trading parties.
- Wallet addresses are used only for the specific transaction, reducing the risk of blockchain analysis linking multiple purchases to a single entity.
This comprehensive framework of anonymity does more than just protect privacy; it establishes the basic trust required for commerce in an environment without legal recourse. It empowers users to engage in transactions with a significantly reduced risk of personal exposure, which is the cornerstone upon which the reliability and continued operation of these platforms are built. The effectiveness of these privacy measures directly correlates with a marketplace's reputation and its longevity in a competitive and self-regulated space.
Private Crypto Payments for Secure Darknet Trade
The adoption of cryptocurrency is fundamental to the operational security and success of darknet marketplaces. It enables a financial layer that aligns with the core principles of user anonymity and transactional privacy. Unlike traditional banking, cryptocurrency transactions do not inherently link to personal identities, providing a significant barrier against surveillance and financial tracking.
Monero (XMR) has become the preferred standard due to its enhanced privacy features. Its blockchain obscures sender, receiver, and transaction amount details by default, making forensic analysis exceptionally difficult. While Bitcoin (BTC) is still accepted on some platforms, its transparent ledger is a vulnerability; tumbling services or the use of intermediate wallets are considered essential but imperfect steps to increase privacy when using it.
The process is integrated directly into the marketplace escrow system. A buyer receives a unique, one-time wallet address generated by the platform for their specific order. Funds sent to this address are held in escrow until the buyer finalizes the order upon successful receipt, at which point they are released to the vendor. This mechanism not only secures the payment but also builds necessary trust between anonymous parties, reducing the incidence of fraud. The decentralized and irreversible nature of these transactions protects both parties from chargebacks and simplifies the financial workflow, making cryptocurrency an efficient and secure payment solution for this ecosystem.
How Escrow Protects Your Darknet Purchases
Escrow is a fundamental mechanism for trust on darknet marketplaces, acting as a neutral third party in transactions. When a buyer places an order, their cryptocurrency is held by the marketplace's escrow service instead of being sent directly to the vendor. This creates a secure environment where both parties can proceed with confidence. The vendor ships the product knowing the funds are secured, and the buyer can finalize the payment only after confirming the product's satisfactory arrival.
The process typically follows a clear sequence:
- The buyer selects a product and submits payment, which is locked in escrow.
- The vendor is notified and dispatches the order.
- Upon receipt, the buyer has a set period to confirm everything is correct.
- If satisfied, the buyer finalizes the transaction, releasing funds from escrow to the vendor.
Disputes are resolved through a structured moderation system. If a package does not arrive or the product is substandard, the buyer can open a dispute. Both parties present their evidence, such as tracking information or product photos, to a marketplace moderator. The moderator reviews the case and decides to either refund the buyer or release the funds to the vendor. This system effectively reduces fraud and incentivizes vendors to maintain high quality and reliability, as their reputation and revenue depend on successful, dispute-free transactions.
How User Reviews Make Darnet Markets Safer and Better
User reviews form the operational backbone of trust and quality assurance on a darknet marketplace. This system functions as a decentralized and self-regulating mechanism where buyers provide direct feedback on their transactions. The review typically includes detailed information on product purity, accurate weight, shipping speed, and stealth packaging. This collective intelligence allows new buyers to assess a vendor's reliability before making a purchase, effectively crowdsourcing safety and quality control.
A vendor's consistent positive feedback builds a strong reputation, which becomes their most valuable asset. High-rated vendors are incentivized to maintain quality and professional service to protect their standing. Conversely, negative reviews serve as immediate and public warnings about scams, poor product, or bad communication. This transparency creates a competitive environment where quality and reliability are financially rewarded. The review system, therefore, shifts the balance of power toward the buyer, establishing a form of accountability that is critical in an anonymous environment.
The structure of reviews often includes:
- Numerical ratings for product and service
- Descriptive text detailing the experience
- Optional pictures as proof of receipt and product quality
This multi-layered feedback loop ensures that product listings are not merely advertisements but are backed by verifiable community history. It reduces the risk for individual buyers and elevates the overall standard of commerce on the platform. Trust is not assumed but is continuously earned and displayed through this transparent ledger of past performance.

How Tor and PGP Keep Your Darknet Trades Safe
The operational security of a darknet marketplace is fundamentally dependent on two complementary technologies: Tor hidden services and PGP encryption. These systems work in tandem to protect both the platform's infrastructure and the private communications of its users, creating a necessary environment for anonymous commerce.
Access to a marketplace is provided through a .onion address, which is a Tor hidden service. This architecture ensures that neither the server's physical location nor the IP addresses of its visitors are exposed on the public internet. All traffic between a user's Tor Browser and the marketplace is encrypted and routed through multiple relays, anonymizing the connection. This makes it exceptionally difficult for any third party to determine who is visiting the site or where the site itself is hosted, providing a foundational layer of network anonymity.
While Tor protects the connection, the content of messages must also be secured. This is achieved with Pretty Good Privacy (PGP), specifically its public-key cryptography. Every transaction relies on this for secure communication:
- A vendor's public PGP key is listed on their profile, allowing buyers to encrypt their delivery address before sending it.
- Only the vendor, who holds the corresponding private key, can decrypt this sensitive information.
- All other order details and support tickets should also be encrypted, ensuring that even marketplace administrators cannot read private data.
This practice of end-to-end encryption means that personal information is never stored or transmitted in plain text. It effectively removes the marketplace as a central point of failure for data leaks. A reliable vendor will always use PGP and will often include a signed message in their profile to verify their identity, preventing impersonation scams. The combined use of Tor for anonymity and PGP for confidentiality forms a robust security model that empowers users to manage their own privacy and engage in transactions with significantly reduced risk of exposure.
How Stable Darknet Markets Build Trust for Safer Trade
Market stability on the darknet is not a given; it is a direct result of operational security and consistent vendor performance. Long-running marketplaces establish their reputation through transparent escrow systems and a robust user review mechanism. These platforms demonstrate stability by processing transactions reliably over extended periods, often surviving through iterative security improvements and maintaining a consistent vendor base. The escrow service holds the buyer's cryptocurrency until the product is received and confirmed, which directly mitigates the risk of fraud and builds a foundation for trust.
In contrast, exit scams are a primary destabilizing factor. These occur when marketplace administrators accumulate a large amount of held funds in escrow and then abruptly shut down the site, stealing all the cryptocurrency. The differences between a stable platform and a potential scam are often visible through community feedback and operational patterns. Indicators of a reliable marketplace include:
- A consistent and verifiable history spanning multiple months or years.
- Active forum discussions and independent reviews beyond the market's own website.
- Transparent fee structures and clear dispute resolution policies.
- Vendors with long-standing, high-positive feedback scores.
Scam sites frequently exhibit the opposite traits: they appear with exaggerated promises, lack a visible history for administrators, and may pressure users with limited-time offers. The stability of a darknet marketplace is therefore a practical assessment of its financial safeguards and community validation, not merely its uptime. A stable market reduces transaction risk for all parties, making the overall environment more predictable and secure for anonymous commerce.